In this article, we list the best five privacy-centric Linux Distributions of 2024 to give you a heads-up before choosing one.
Internet privacy has become a major concern with the Pandemic and work-from-home situations. The more we go deep into the digital edge, the more cyber security and privacy become a considerable aspect of everyone’s daily life. Almost every day, you see CVEs, a couple of zero-day in a month and ransomware attacks.
Fortunately, Linux is generally secured by design if you compare it with Windows. In addition, most Linux distributions are secure if you follow some best practices while using them for your day-to-day work.
Besides, some specific Linux Distributions give you an additional layer of security with extra tools for your work and personal usage. For example, suppose you want complete anonymity on the internet or are a cyber security expert. In that case, you may consider something other than popular mainstream Linux distros such as Ubuntu or Fedora.
Here’s a list of 5 Linux distributions that offer better privacy and protection for users.
Table of Contents
Top Privacy Specific Linux Distributions in 2024
Tails
The Amnesic Incognito Live System (in short, Tails) is a Debian-based Linux distribution which gives you complete anonymity over the Internet while you browse the web. It primarily uses the Tor network designed to redirect traffic via its network to conceal your location and other private information. In addition, it comes with all necessary secure applications that deal with email, browsers and other tools.
If you need a Linux Distribution that gives you complete privacy built-in, then Choose Tails.
Advantages
- Well integrated with the Tor network
- Browser is pre-configured with NoScript, HTTPS anywhere and other related add-ons (Firefox)
- Built-in Bitcoin wallet, wireless network audit tool and comes with Onion Circuits
- LIVE medium
More details about Tails
- Home page: https://tails.boum.org/
- Release frequency: 5 to 6 releases per year
- Distro type: Debian (Stable), GNOME, LIVE Medium, 64-bit only, x86_64
- Download: https://tails.boum.org/install/index.en.html
Parrot OS
Parrot (earlier known as Parrot Security OS) is also a Debian-based Linux distribution primarily designed for cyber security professionals and pen-testers who want a complete Linux distro that gives them all the tools they need.
Moreover, you can easily use it for your daily driver with built-in sandboxing options primarily used for digital forensic work. On top of that, it can connect to other devices using its containerisation technologies.
Advantages
- Debian-based and Live system
- Choice of wide-range desktop flavours
- Applications that run are sandboxed
- Perfect for digital forensic work
More details about Parrot OS
- Home page: https://parrotsec.org/
- Release frequency: 2 to 3 releases per year
- Distro type: Debian (Testing), MATE & KDE Plasma, LIVE Medium, 64-bit only, x86_64
- Download: https://parrotsec.org/download/
Qubes OS
The Qubes OS is a unique Linux distribution based on Fedora Linux. Qubes provides multiple “virtual machines” or “Qubes” that host the applications. The approach effectively isolates the “personal”, “work”, or other user-defined workflows.
Moreover, to differentiate between separate “machines”, this distro provides colour codes to the profiles so that you know which is running what.
In addition, with this approach, if you happen to compromise your identity or download any malware in one “virtual machine”, the rest of the system is safe. This approach is called “security by isolation” and is perfect for tech-savvy and average users requiring privacy over the internet.
Advantages
- “security by isolation” with stand-alone “virtual machines”
- Built-in sandboxing support
- Offers full disk encryption
- Colour-coded “Qubes” for easy workflow navigation
More details
- Home page: http://qubes-os.org/
- Release frequency: 2 to 3 releases per year
- Distro type: Fedora, Xfce, Desktop, 64-bit only, x86_64
- Download: https://www.qubes-os.org/downloads/
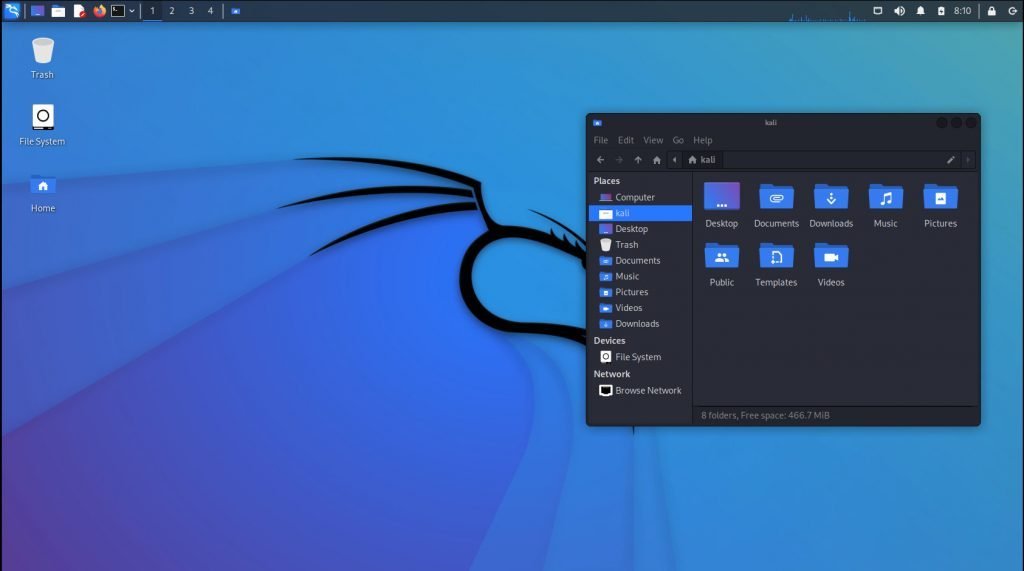
Kali Linux
Kali Linux is the most popular penetration-testing Linux distribution on this list based on the Debian testing branch. Named after the Hindu goddess “Kali”, this Linux distribution comes with 32-bit, 64-bit and ARM versions for Raspberry Pi and other devices. On top of that, it comes with a vast set of tools giving security researchers and cyber experts an advantage over other distributions.
Here’s why it’s popular
- Kali Linux is almost an “industry standard” distro for security researchers
- Full disk encryption
- i686, x86 and ARM support
- LIVE system
- Well-made documentation with a training suite for customising Kali Linux for specific research
- Kali Linux provides paid certification course for pen testing
More details about Kali Linux
- Home page: http://www.kali.org/
- Release frequency: 3 to 4 releases per year
- Distro type: Debian (Testing), GNOME, KDE Plasma and others, Desktop & Live and others, 32-bit and 64-bit, x86_64, i686, ARM
- Download: http://www.kali.org/downloads/
Whonix Linux
Whonix is another uniquely designed Linux distribution based on Debian. It runs as a virtual machine inside VirtualBox, effectively giving an operating system that can not reside on disk whereas not lost after multiple reboots.
Moreover, its unique design provides a gateway component which connects to the Tor network. And a second component is called a workstation which runs all the user applications. These user applications connect to the gateway, which gives the applications and users complete anonymity. Finally, this unique two-phase isolation approach gives you complete privacy while mitigating several risks.
Reasons why Whonix is one of the best privacy-centric distros
- Two-phased isolation, which separates network and user applications
- Tor network support with Tor applications such as the browser and instant messaging
- Pre-loaded with major applications
- Linux Kernel Runtime guard support
More details about Whonix
- Home page: https://www.whonix.org/
- Release frequency: 1 release per year
- Distro type: Debian, Desktop, Xfce, 64-bit, x86_64
- Download: https://www.whonix.org/
Other mentions
In addition to the above list, we would like to mention Linux Kodachi and BlackArch Linux, similar to the above distributions.
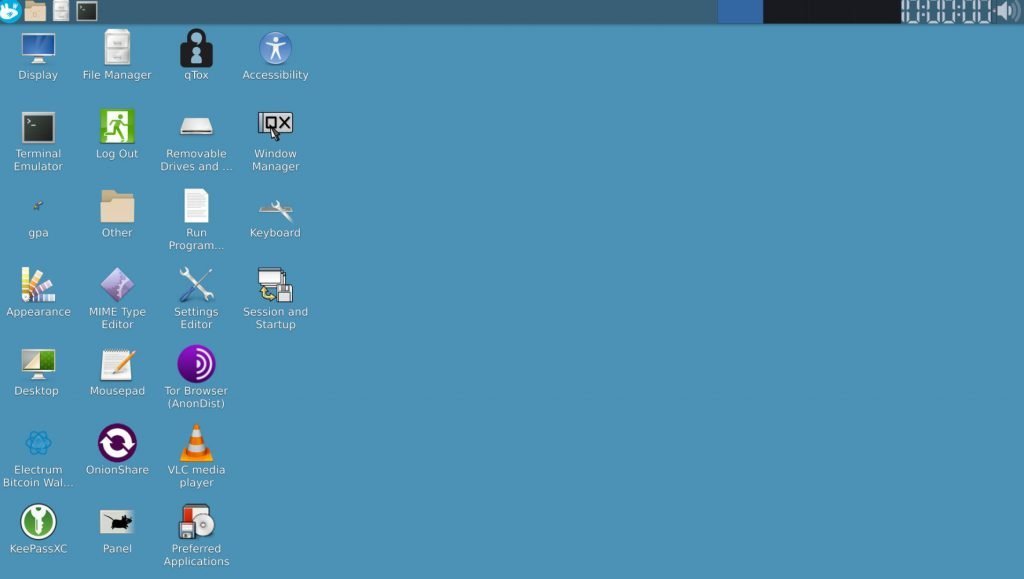
Firstly, Linux Kodachi is also a Debian-based distribution which uses the Tor network to provide privacy to its user. It comes with an Xfce desktop environment and only provides a 64-bit installer.
In addition to Kodachi, the BlackArch Linux is the only one in this list based on Arch Linux. It comes with Window managers (Fluxbox, Openbox) instead of desktop environments and brings over a thousand applications ideal for pen-testing and security analysis.
Closing Notes
Finally, I hope this list of top privacy-focused Linux distributions of 2024 gives you a starting point to protect yourself and your privacy over the internet.
Last but not the list, I would remind you that if you use the above distros with the Tor network, then do not perform any banking or financial transactions (especially those that use multi-factor authentication with mobile verification) using these distributions. Because it routes your traffic via different countries, hence it’s better not to use these for your financial work.
Image credit: respective distro, Wikipedia