Kali Linux is a Debian-based Linux distribution designed for ethical hackers and security professionals. It is pre-installed with a wide range of penetration testing and security auditing tools, making it a powerful platform for identifying and exploiting vulnerabilities.
Over the last few years, Kali Linux has become more popular among security researchers and professionals due to its dedicated focus on providing a complete Linux operating system which comes with the latest and greatest tools in the cybersecurity industry. Today, it is the “go-to” operating system for security professionals.
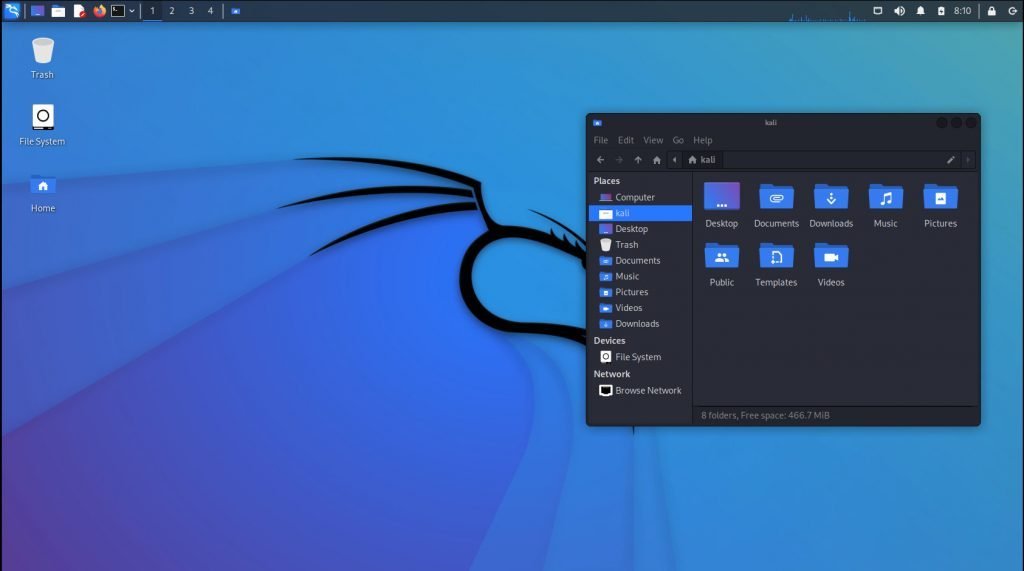
Let’s see what this distribution has to offer.
Table of Contents
Kali Linux Features
Installation
The installation and availability of the OS are important considering users experience information on variety of devices. There are different architectures available as well.
Kali Linux offers pre-compiled ISO and installable images for all architectures and hardware. Here’s a list of architectures and hardware platforms for which you get the Kali Linux installer.
- Standard ISO images
- 64-bit ISO for X86_64 architecture
- 32-Bit ISO for older hardware
- Apple Silicon M1, M2, M3 (ARM64)
- Pre-built images for virtual machines (both 64-bit and 32-bit)
- VMWare
- VirtualBox
- Microsoft Hyper-V
- QEMU
- Vagrant boxes
- ARM
- Apple Silicon
- Raspberry Pi
- Pinebook
- gateworks
As you can see, the support pretty much covers almost all architectures. You might be wondering why. This is because it is based on Debian Linux, which is a “universal operating system”.
Pre-installed tools
The reason why security professionals like Kali Linux is the pre-loaded set of tools ranging in every aspect of information security management. Key highlights of general features include:
- Wide range of pre-installed tools: Kali Linux comes with over 600 penetration testing tools pre-installed, including Nmap, Wireshark, Metasploit Framework, and John the Ripper. This makes it a one-stop shop for security professionals who need to test the security of their networks and systems.
- Open source and free: Kali Linux is an open-source operating system that is free to use and distribute. This makes it a great option for security professionals on a budget.
- Regular updates: Kali Linux is updated with new tools and security patches. This helps to ensure that the operating system is always up to date with the latest threats.
- Customizable: Kali Linux is highly customizable, so security professionals can tailor the operating system to their needs. This can be done by installing additional tools, configuring the operating system, or creating custom scripts.
In addition to these general features, Kali Linux also has a number of other features that are specifically designed for ethical hackers, such as:
- Live USB boot: Kali Linux can be booted from a live USB drive, which means that it can be run without having to install it on a hard drive. This is useful for security professionals who need to test the security of a system without making any permanent changes.
- ARM support: Kali Linux supports ARM processors, which means that it can be run on a wide range of devices, including smartphones and tablets. This makes it a versatile platform for security professionals who need to test the security of mobile devices.
- Release cadence: Kali Linux behaves like a rolling release distribution (based on Debian testing), which means that new updates are released continuously. This ensures that security professionals always have access to the latest tools and security patches. This is very important when you are dealing with system vulnerability discovery.
Things you can do with Kali Linux
Here are some specific examples of how Kali Linux can be used:
- Penetration testing: Security professionals can use Kali Linux to perform penetration tests, which are simulated attacks that are designed to identify and exploit vulnerabilities in a system.
- Security auditing: Kali Linux can be used to conduct security audits, which are comprehensive assessments of a system’s security posture.
- Malware analysis: Kali Linux can be used to analyze malware, which is software that is designed to harm a system or its users.
- Vulnerability research: Security professionals can use Kali Linux to conduct vulnerability research, which is the process of discovering and analyzing vulnerabilities in software and systems.
Things you should not do with Kali Linux
There are a few misconceptions about Kali Linux use cases. Due to this, many beginners in the Linux world try to first try Kali Linux with the hope of starting hacking immediately.
But it is entirely wrong.
First of all, Kali Linux is NOT a beginner Linux distribution. If you are trying Linux or trying to install Linux for the first time, don’t use Kali Linux. Get your hands on the Linux Mint or Ubuntu, or something similar. Then try Fedora Linux for a bit. Probably after that, you can give Kali Linux a try.
Secondly, Kali Linux provides all the tools for you. But if you don’t know what you are doing or do not have any concept of networking (wired or wireless), operating system internals and so on, then those tools aren’t helpful for you.
That said, if you are a student or a new Linux user, it is not recommended to try Kali Linux. Try it after some experience with other beginner-friendly distributions.
Changing with the times
As the technology changes, the behaviour of vulnerabilities and attack vectors changes. With these, the Kali Linux team continuously updates the distributions with new tools to assess and mitigate those new areas.
Here are some of the latest features introduced in Kali Linux in this regard:
- Calico is a cloud-native networking and network security solution that provides a suite of tools for managing and securing Kubernetes deployments.
- cri-tools is a set of CLI and validation tools for the Kubelet Container Runtime Interface (CRI). This interface allows Kubernetes to communicate with different container runtimes, such as Docker and containers.
- Hubble is a network, service, and security observability tool for Kubernetes that uses eBPF to provide real-time visibility into your cluster.
- ImHex is a Hex Editor for reverse engineers, programmers, and people who value their retinas when working at 3 AM.
- kustomize is a tool for customizing Kubernetes YAML configurations. It makes it easier to manage and apply changes to your deployments, and it can also be used to create reusable components.
- Rekono is an automation platform that combines different hacking tools to complete pen-testing processes. It can be used to automate tasks such as vulnerability scanning, exploitation, and reporting.
Education and Community
One of the great contributions of Kali Linux to the community is its study materials, documentation and certifications for budding security professionals.
Kali Linux documentation is one of the best for the segment. You can learn via its portal for hundreds of tools.
They also provide Kali Linux Certified Professional (KLCP) certification, which is a great addition for students or job-seekers who want to make a career in cyber security.
Most of the documentation is free to read and study.
Closing Notes
Kali Linux is a powerful Linux distribution that can be used for a variety of purposes. However, it is important to use Kali Linux responsibly and ethically. Security professionals should only use Kali Linux to test the security of systems they have permission to test. They should also be careful not to cause any damage to the systems that they are testing.
However, if you want a career or learn cyber security – it is the best free and open-source distribution available as a complete package.
You can start by installing Kali Linux in a Virtual machine and go from there.
Cheers.