A few points why Kali Linux is used by most of the hackers and pen testers.
Kali Linux is a Debian “testing” based Linux operating system created almost a decade ago. Over the last few years has gained significant popularity among hackers and cybersecurity professionals. With the ever-increasing dependency on digital infrastructures and ever-growing online threats, cybersecurity has become more relevant today for average users and businesses.
Ethical hackers and penetration testers play a vital role in identifying vulnerabilities and strengthening the security of systems. Kali Linux has emerged as their go-to operating system due to its comprehensive tools and features tailored for security testing and analysis.
Table of Contents
Overview
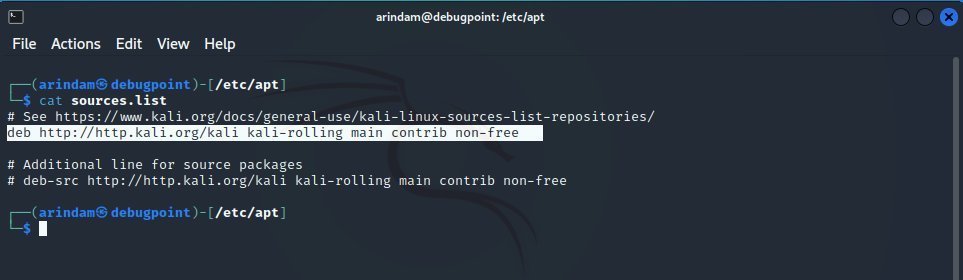
Kali Linux is maintained by Offensive Security, an American information security company and contributed by thousands from the community. It follows the Debian “testing” branch, which remains up to date with bleeding edge packages to provide hackers with the latest modules for their work.
In addition, it supports multiple architectures such as x86, x86-64, armel and armhf – which helps hackers using a wide hardware spectrum.
One of the best advantages of using this distro is that it is available for multiple tech platforms, which you can download and use. Here are some of them:
- 32-bit and 64-bit installer images (ISO)
- Virtual machine pre-built images
- ARM images
- Android images for mobile devices
- Docker and LXD images
- Cloud availability from various vendors
- Read only LIVE ISO images
- Available on Windows Subsystem for Linux (WSL)
Reasons why it is preferred
Powerful Penetration Testing Tools
Kali Linux offers a vast arsenal of penetration testing tools that enable hackers to identify and exploit vulnerabilities. These tools range from network scanners and password crackers to wireless attack frameworks and web application assessment utilities. The availability of such tools within a single operating system greatly simplifies the workflow of hackers, allowing them to focus on their objectives effectively.
Comprehensive Security Assessments
With this distribution, hackers can perform comprehensive security assessments on various targets. They can simulate real-world attacks, analyze system weaknesses, and devise effective security strategies. The operating system provides tools for vulnerability scanning, network mapping, and system fingerprinting, enabling hackers to assess the security posture of target systems from different angles.
Forensic Analysis and Incident Response
Kali Linux also includes tools for digital forensics and incident response. Hackers can leverage these tools to investigate security breaches, gather evidence, and analyze compromised systems. The operating system supports data recovery, memory analysis, and network forensics, facilitating thorough investigations and aiding in the recovery of compromised systems.
Wireless Network Auditing
Wireless networks are often a prime target for hackers due to their inherent vulnerabilities. Kali Linux offers comprehensive tools for auditing and securing wireless networks. Hackers can use these tools to identify weak encryption protocols, discover hidden networks, and perform packet analysis to detect malicious activity. This allows them to assess the security of wireless networks and propose mitigation strategies.
Vast list of Tools
Here’s a brief list of tools categories which are available by default (as of the latest release):
- Information gathering
- DNS analysis
- IDS/IPS identification
- Live host identification
- Network and port scanner
- OSINT analysis
- Route analysis
- SMB analysis
- SMTP analysis
- SNMP analysis
- SSL analysis
- Vulnerability analysis
- Fuzzing tools
- VoIP tools
- Web application analysis
- CMS and framework identification
- Web application proxies
- Web crawlers and directory bruteforce
- Web vulnerability scanners
- Database assessment
- SQLite database browser
- Password attacks
- Offline attack tools
- Online attack tools
- Passing the hash tools
- Password profiling and word lists
- Wireless attacks
- 802.11 Wireless tools
- Bluetooth attack tools
- Reverse engineering tools
- Clang
- NASM shell
- Exploitation tools
- Metasploit
- Searchsploit
- MSF payload creator
- Social engineering toolkit
- Sniffing and spoofing
- Network sniffers
- Spoofing and MITM
- Post exploitation
- Forensics
- Forensic carving tools
- Forensic imaging tools
- PDF forensics tools
- Sleuth kit suite
- Reporting tools
- Cutycapt
- Faraday start
- Pipal
- Social engineering tools
You can learn more in the comprehensive tools portal:
Being open-source
One of the primary reasons why hackers prefer Kali Linux is its open-source nature. Being an open-source operating system, it allows hackers to access and modify the source code as per their requirements. This grants them the freedom to customize the system and add their own tools or functionalities. The open-source community also actively contributes to developing and improving Kali Linux, ensuring that it stays up-to-date with the latest security techniques and technologies.
Community Support and Collaboration
Kali Linux has a vast supportive community of security professionals, hackers, and enthusiasts. This community actively collaborates to enhance the operating system’s capabilities by sharing knowledge, developing new tools, and providing support to fellow users.
The availability of forums, online tutorials, and community-driven documentation ensures that hackers using Kali Linux can access valuable resources and seek assistance whenever needed.
The team also provides several training and learning mediums. These also have a learning path for students who want to pursue a career in cybersecurity, including certifications.
Customization and Flexibility
Another advantage is its high degree of customization and flexibility. Hackers can tailor the operating system to suit their specific needs and preferences. They can install and configure tools as per their requirements, create custom scripts, and build personalized workflows. This level of customization allows hackers to optimize their productivity and streamline their penetration testing processes.
Continuous Updates and Improvements
Kali Linux is a dynamic operating system that undergoes continuous updates and improvements. The developers and community members actively work on enhancing existing tools, adding new features, and addressing any security vulnerabilities. These updates ensure that hackers using Kali Linux have access to the latest tools and techniques, keeping them at the forefront of cybersecurity advancements.
Ethical Use
It is important to note that Kali Linux is intended for ethical hacking and security testing purposes. Ethical hackers use their skills to identify vulnerabilities and protect systems, not to engage in malicious activities.
Kali Linux promotes the responsible and legal use of hacking tools, emphasizing the importance of obtaining proper authorization and adhering to ethical guidelines. The operating system is a powerful tool for cybersecurity professionals to enhance organisations’ security and contribute to a safer digital landscape.
In a nutshell, DO NOT USE Kali Linux for illegal or unauthorised usage.
Conclusion
I hope this overview introduces Kali Linux and why it is a preferred free and open-source operating system by security professionals worldwide. Its Debian base, armed with thousands of tools and easy access, makes it a compelling choice for everyone.
You can download Kali Linux on the official website.